Cyber security consulting—how they help to ke...
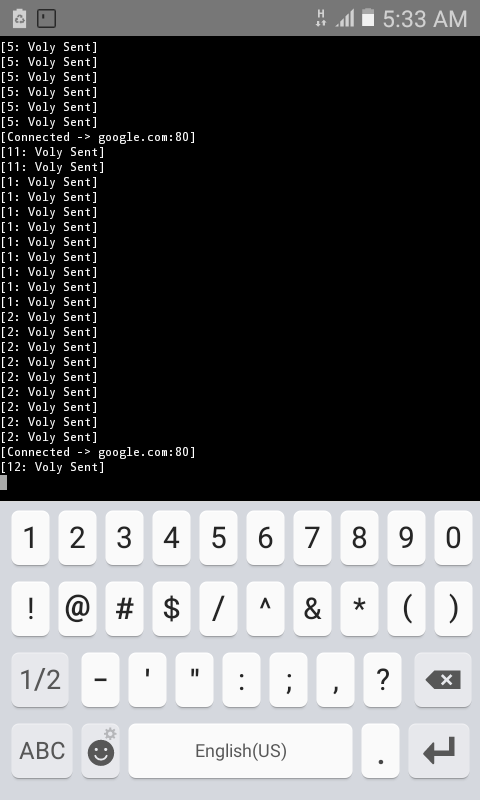
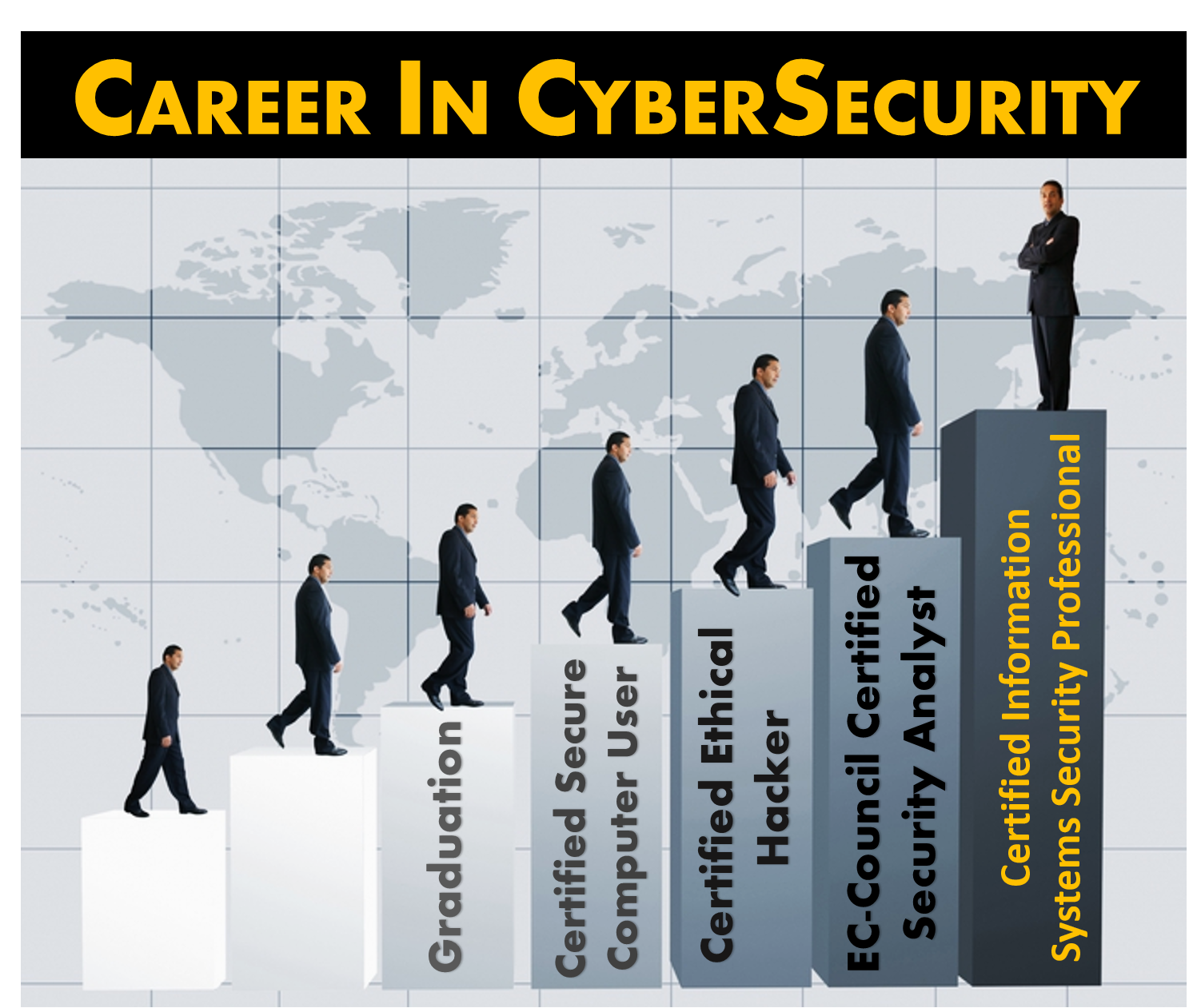
Computer or cyber security or information technology security is actually the protection process of the computer systems and the networks from the dangers of disclosure of information or theft or damage to their hardware, electronic data...