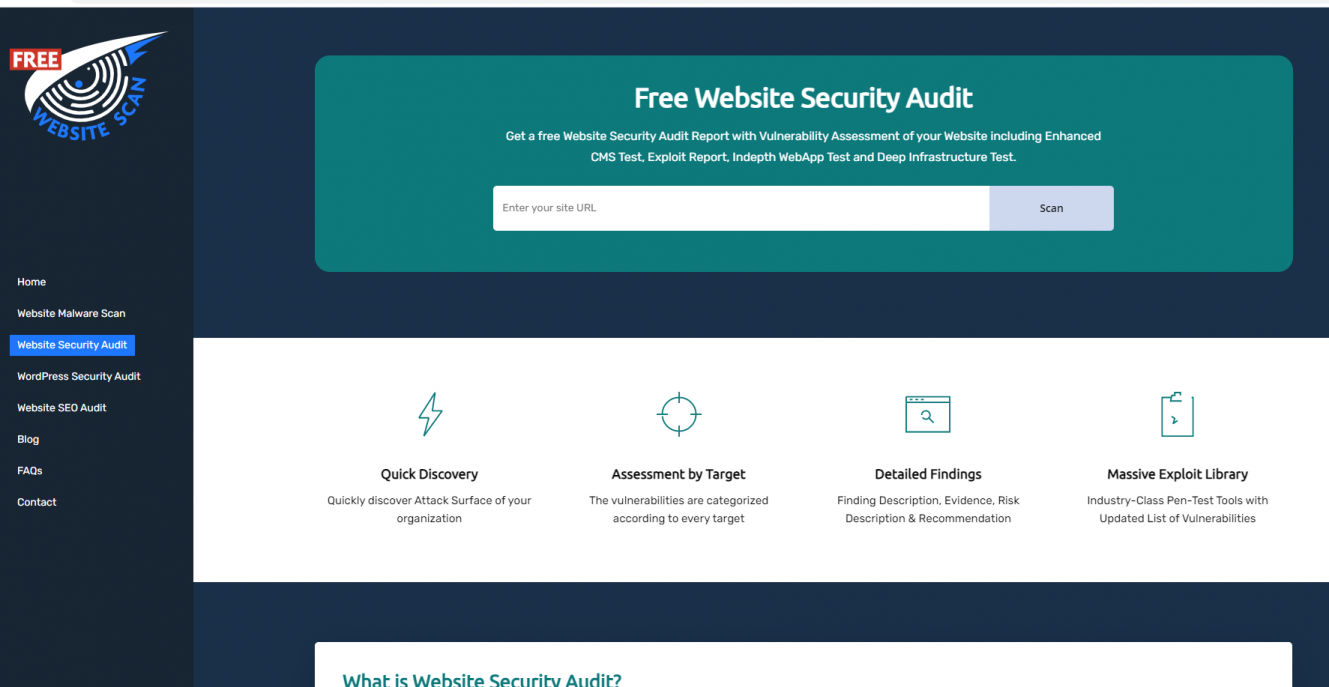
Website Security Audit Systems provides a Continuous Source of Protection (CSP). This service is particularly for those who take online security quite seriously and require the best in constant protection
A website security audit is one of the most effective ways to protect your online presence from attacks. It thoroughly tests your site for potential or existing vulnerabilities that hackers could exploit. It includes your entire website structure, from its route database to scripts, themes, extensions, hosting server settings, configuration, SSL installation, and so on. This thorough check is a vital measure used to determine what type of vulnerabilities exists on your website, in order to what steps you need to take to fix them.
There are two types of website security audits: manual and automated. A manual audit involves searching through your site for any vulnerabilities. For every vulnerability, there will probably be at least some documentation that describes the problem and the way to exploit it. These documents could also be included in your software distribution.
The automated scan finds the vulnerability, then analyzes it. Based on the severity of the vulnerability, the program performs a first step verification. For example, if there is a cross-site vulnerability, the program may try to download a virus scanner first. If that doesn't work, it searches for vulnerable versions of PHP and Perl. When a match is found, then the program performs a manual penetration test, to determine whether the site is actually vulnerable or not.
Before running a website security audit, make sure that the scanning software can identify all types of threats to your site. The first step should be performing a manual verification to make sure the scan is comprehensive. You should run the test multiple times and take note of the results. Once you've identified all possible security issues with your site, you can start the second step of testing.
The next thing to do is to connect to a remote machine and run a series of tests from there. For our website security audit, we had two computers: one with a webserver, and one without. Using the map command in our webserver, we connected to the other computer and performed an nmap against our target domain. Using the -scan option, we also specified the interface that we were using (we used Nmap). That way, the following command would return a list of all scanned interfaces.
After running the scanning, we saved all results in text files. We then went ahead and opened the files in an editor to verify the results. To ensure better efficiency of the scanning and the identification of potential security issues, we wrote a series of best practices to follow while conducting website security audits.
The first step of conducting a web security audit is to create a list of vulnerabilities. For this, we based our list on the most common vulnerabilities that can affect your website. It may include: SQL injection, cross-site scripting, cross-site exploits, cross-site scripting vulnerability, file uploading, file download failure, page height bugs, and many more. By listing all these vulnerabilities, you will be able to determine which among them is the most critical and needs further monitoring.
For the second step of the website security audit, we tested for each vulnerability on a particular site. By performing a detailed scanning on one site, we will be able to pinpoint the issues that may affect other sites. In addition, by performing an exhaustive website security audit, you will be able to identify all the security flaws that exist in your application and/or infrastructure. Lastly, for the third step of the process, we applied any patches or updates that we found after completing the full website security audit.
This kind of service means that businesses are more aware of threats and vulnerabilities and take steps to prevent these issues from becoming a problem.
The CSP services offered by a good website security audit company should always include daily site scans, web crawls and other types of scans to keep your website and your business as safe as possible. The daily site scans will monitor the health of your web pages and any changes made to these pages. These daily scans will make sure that no harmful scripts or malware are infecting your system and causing problems. The daily site scans also will check for outdated content, spyware, Trojans, phishing attacks, adware and other forms of Spyware, which can compromise your system and your data if it is not cleaned on a regular basis. These scans also will check for scripts which could be causing issues with your website and your business, as well as scripts which could be running on your system without your knowledge or consent. If you feel that some scripts are causing issues then you should make sure that you remove them straight away.
For the web crawlers, this kind of service is invaluable, as they can easily identify vulnerable areas of your website using various algorithms. In order for a CSO to assess the risk of your website, he will have to look at a number of different factors. These factors can include attack methods, weak spots in the site, any method of exploitation he may find, vulnerable database entries and so forth. With the daily Site Scan, an SEO can make sure that these risks are all removed and that your entire website using the services has a much higher chance of being scanned than before. This means that you will have more visitors, a better ranking and a better performance from search engines.